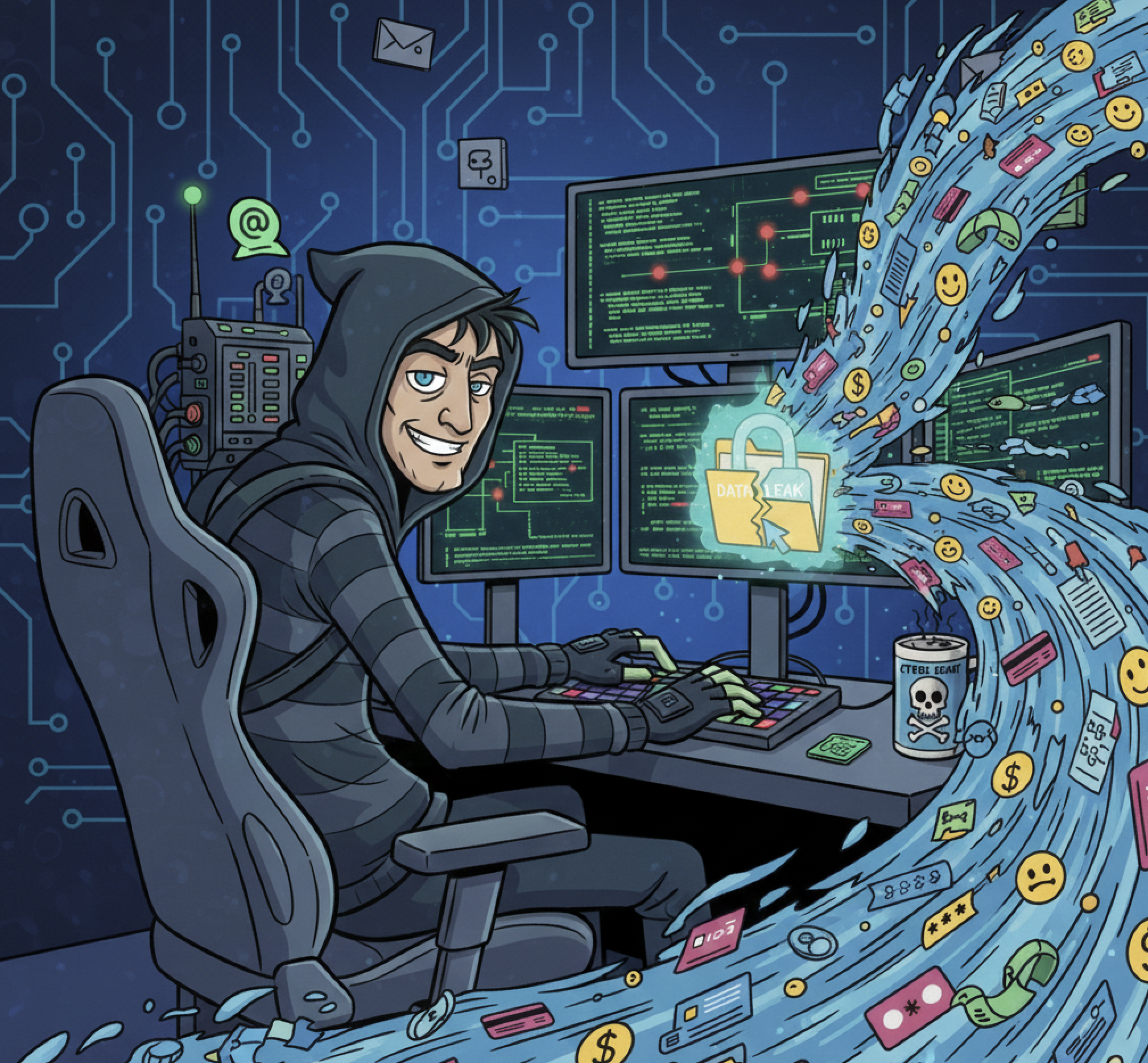
ADT confirms data breach after ShinyHunters leak threat
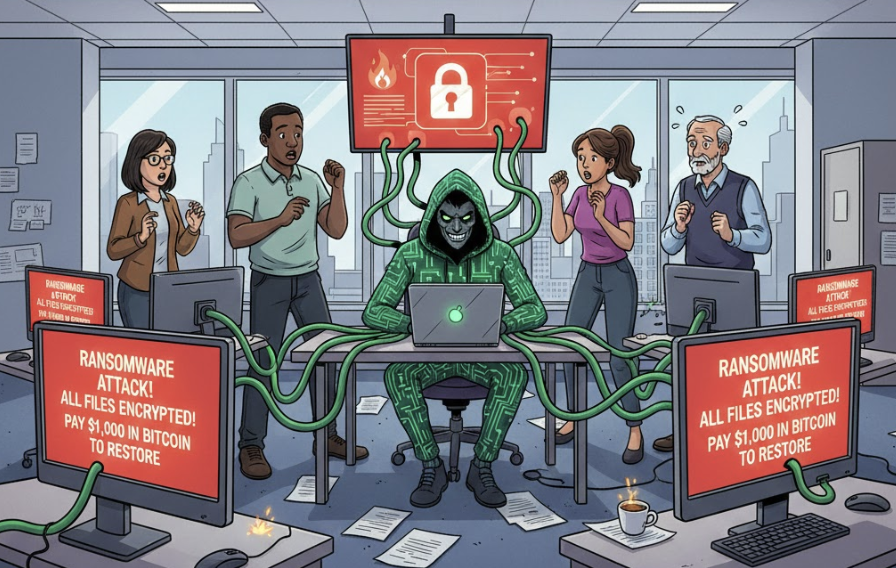
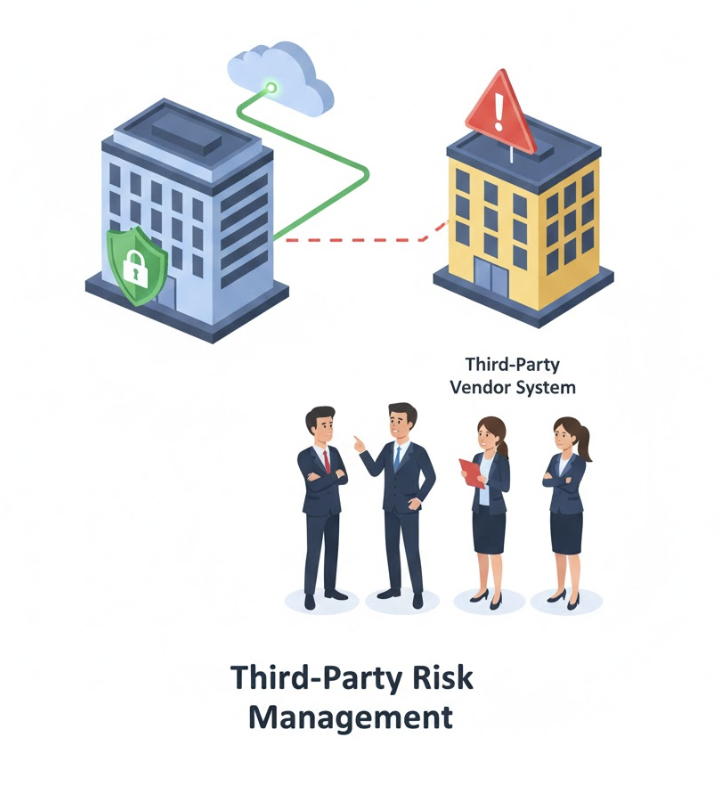
Home security company ADT suffered a cyberattack where criminals stole customer data and are now demanding ransom money to prevent its release. If you're an ADT customer, watch for any notifications from the company about this breach and monitor your accounts for suspicious activity.